Cisco 350-201 CBRCOR Dumps
350-201 CBRCOR Performing CyberOps Using Cisco Security Technologies v1.0 is the core exam of Cisco Certified CyberOps Professional certification. PassQuestion new cracked Cisco Certified CyberOps Professional 350-201 CBRCOR Dumps which cover all the objectives with real questions and answers to help you best prepare for your Cisco 300-201 Exam. If you study hard on PassQuestion Cisco Certified CyberOps Professional 350-201 CBRCOR Dumps, we guarantee you will pass your Cisco 350-201 CBRCOR exam successfully in your first try. You also can get latest 300-215 CBRFIR dumps from PassQuestion to achieve your certification.
350-201 CBRCOR Exam Description
Performing CyberOps Using Cisco Security Technologies v1.0 (CBRCOR 350-201) is a 120-minute exam that is associated with the Cisco CyberOps Professional Certification. This exam tests a candidate's knowledge of core cybersecurity operations including cybersecurity fundamentals, techniques, processes, and automation.
To earn Cisco Certified CyberOps Professional certification, you pass two exams: one that covers core technologies 350-201 Performing CyberOps Using Cisco Security Technologies (CBRCOR) and one concentration exam 300-215 Conducting Forensic Analysis and Incident Response Using Cisco Technologies for CyberOps (CBRFIR). And every exam in the program earns an individual Specialist certification, so you get recognized for your accomplishments along the way.
350-201 CBRCOR Exam Information
Exam Code: 350-201 CBRCOR
Exam Name: Performing CyberOps Using Cisco Security Technologies v1.0
Certification: Cisco Certified CyberOps Professional, Cisco Certified CyberOps Specialist – CyberOps Core
Duration: 120 minutes
Available languages: English
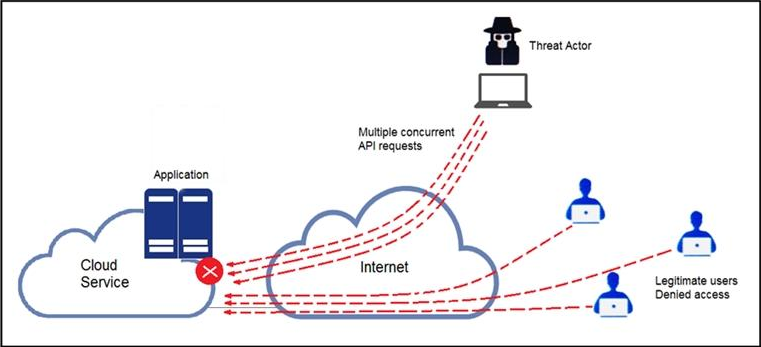
Exam Topics
View Online Cisco Certified CyberOps Professional 350-201 Free Questions
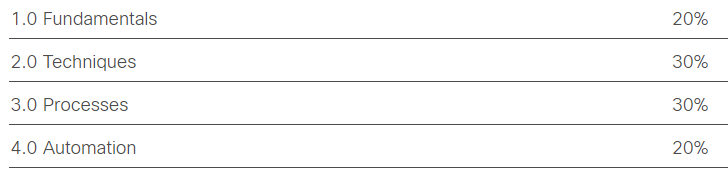
1.Refer to the exhibit.
A threat actor behind a single computer exploited a cloud-based application by sending multiple concurrent API requests. These requests made the application unresponsive.
Which solution protects the application from being overloaded and ensures more equitable application access across the end-user community?
A. Limit the number of API calls that a single client is allowed to make
B. Add restrictions on the edge router on how often a single client can access the API
C. Reduce the amount of data that can be fetched from the total pool of active clients that call the API
D. Increase the application cache of the total pool of active clients that call the API
Answer: A
2.A threat actor attacked an organization’s Active Directory server from a remote location, and in a thirty-minute timeframe, stole the password for the administrator account and attempted to access 3 company servers. The threat actor successfully accessed the first server that contained sales data, but no files were downloaded. A second server was also accessed that contained marketing information and 11 files were downloaded. When the threat actor accessed the third server that contained corporate financial data, the session was disconnected, and the administrator’s account was disabled.
Which activity triggered the behavior analytics tool?
A. accessing the Active Directory server
B. accessing the server with financial data
C. accessing multiple servers
D. downloading more than 10 files
Answer: C
3.The physical security department received a report that an unauthorized person followed an authorized individual to enter a secured premise. The incident was documented and given to a security specialist to analyze.
Which step should be taken at this stage?
A. Determine the assets to which the attacker has access
B. Identify assets the attacker handled or acquired
C. Change access controls to high risk assets in the enterprise
D. Identify movement of the attacker in the enterprise
Answer: D
4.A new malware variant is discovered hidden in pirated software that is distributed on the Internet. Executives have asked for an organizational risk assessment. The security officer is given a list of all assets.
According to NIST, which two elements are missing to calculate the risk assessment? (Choose two.)
A. incident response playbooks
B. asset vulnerability assessment
C. report of staff members with asset relations
D. key assets and executives
E. malware analysis report
Answer: BE
5.Refer to the exhibit.
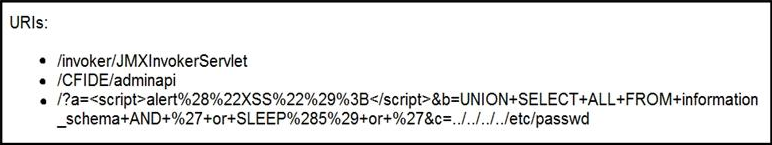
At which stage of the threat kill chain is an attacker, based on these URIs of inbound web requests from known malicious Internet scanners?
A. exploitation
B. actions on objectives
C. delivery
D. reconnaissance
Answer: C
Comments
Post a Comment